Windows 7 stuck identifying network
We've recently been deploying a new backup agent to various machines. The engineer doing the deployment reported to me, that around 40 of the 140 Windows 7 machines, which act as print servers, were refusing the backup agents connections. First I checked the Group Policies, and ensured the Firewall rule had been added. I then checked and all of the machines were in the correct container, so I hopped on to one of the failing machines to take a look.
I first went to the Firewall, and sure enough I could see the rules allowing the connection, but then I noticed that the active profile was Public instead of Domain.
Not your usual culprits###
At first I assumed that there was a mis-configuration on the network connection. I opened network and sharing centre, and sure enough, there was an endless spinning "Identifying" notification.

Assuming there must be a DNS or Default Gateway issue, I ran ipconfig.
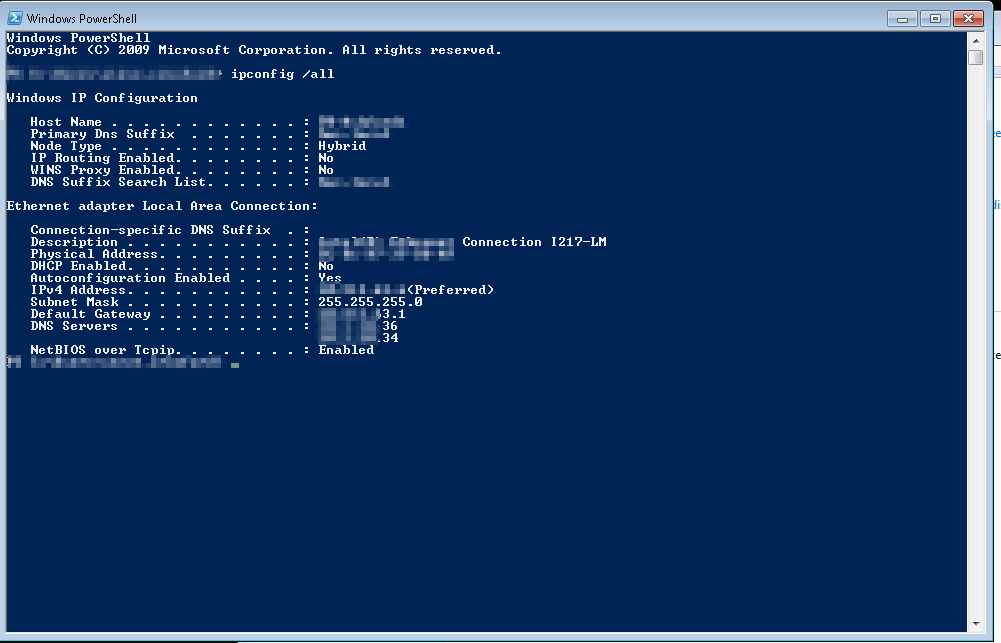
However all of those settings were correct. So I went digging through log files trying to determine what could be causing the identification to fail, but there was no relevant information.
I then turned to the internet, and found various suggestions around reinstalling network drivers and changing local security policies, but none of them applied, so I went to TechNet and started reading anything I could about how the Network identification (Network Location Awareness) works.
The Fix###
Technet explains that the very first thing Network Location Awareness(NLA) does, is check if the connection specific suffix matches a value stored in the registry. If the value matches, NLA attempts an Ldap connection to a Domain Controller, which if also successful, results in the domain profile being loaded. As I had already checked the network connection, I headed to the registry key HKEY_Local_Machine\Software\Microsoft\Windows\CurrentVersion\Group Policy\History\NetworkName and found this:
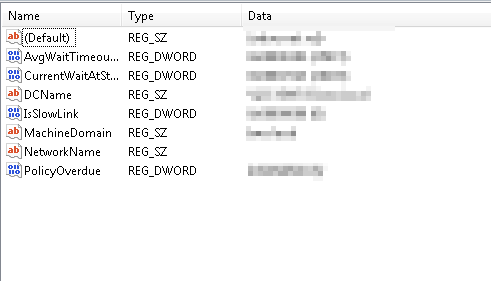
Yes! the NetworkName key has no value! So I set it to the correct value of the domain name, and rebooted the machine. Sure enough once the machine had restarted, the network identified instantly, the correct firewall profile loaded, and the agent was able to connect.
I then proceeded to check a few more of the machines, and discovered all of the failing machines had the missing value, where as all of the working machines had the correct value.
Finish with some PowerShell###
Not wanting to log onto 40 machines and edit the registry manually, I put together a small script, to run on all of the failing servers.
$registryPath = "HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy\History"
$name = "NetworkName"
$value = "<THE CORRECT NETWORK NAME>"
if(-not (Get-ItemProperty -Path $registryPath -Name $name).$name){
New-ItemProperty -Path $registryPath -Name $name -Value $value -PropertyType String -Force | Out-Null
}
